https://www.gpg4win.org/package-integrity.html
Hello, I am trying to verify whether or not my download is valid. While the serial number and issuer are valid, I cannot find the rest of the things mentioned on the website (like sha1_fpr and md5_fpr) in the digital certificate. My download is the right size. If I assume the notBefore and notAfter parts of the signature on the website are ‘Valid from’ and ‘Valid to’ on my digital certificate, it is exactly one hour off. The ‘Subject’ part of the website is different to my certificate’s subject: https://anonfile.com/b49cPct3n5/Subject_Comparison_PNG
Here’s literally every property compared with the other: https://anonfile.com/1cI7Qbtan1/Capture_PNG, https://anonfile.com/C0I9Q1t8n0/Capture_PNG, https://anonfile.com/s1J4Qctenf/Capture_PNG, https://anonfile.com/78J5Q5tbna/Capture_PNG, https://anonfile.com/F3J3Q4t6nd/Capture_PNG, https://anonfile.com/QaJ1Qatan7/Capture_PNG, https://anonfile.com/gcK6Q2tanf/Capture_PNG, https://anonfile.com/u8K4Q2t0n8/Capture_PNG, https://anonfile.com/56KeQ0t6n3/Capture_PNG, https://anonfile.com/I9KbQ4tfna/Capture_PNG, https://anonfile.com/P8K5Qat6n3/Capture_PNG, https://anonfile.com/A2LbQ2t1n8/Capture_PNG.
By the way, https://wiki.gnupg.org/Gpg4win/CheckIntegrity doesn’t explain what exactly should the ‘expected publisher’ be, and it says to check the ‘file properties’ without even saying what properties indicate a valid download.
The SignTool command is not downloadable for Windows 10, which I have because I got my computer before I was interested in privacy.
Help me please? I’m completely new to GnuPG and the only reason I’m getting into it is so I can securely download QubesOS.
Hi,
In general for codesigning you can leave it to the Operating System to do the signature verification. If it shows it as validly signed you are good. If you do not trust your operating system to do even that then it can’t securely install updates for other software or itself etc. and you have already lost.
Manual checking is mostly needed when something goes wrong with that. E.g. if our Root CA is not available.
For the certificate itself all the properties you have checked are basically of no security value. The important thing is the “Thumbprint” (usually called fingerprint). This should match our Certificate. Then you can be sure it is the right one. On the package integrity page it is called sha1_fpr.
https://cdn-03.anonfile.com/P8K5Qat6n3/ab347115-1559628610/Capture.PNG
So from your screenshot I can see that you have the right one.
Once you have installed Gpg4win the first time you can use our OpenPGP signatures for manual checking of future updates.
And yes the wiki page can be improved. But as I said in the first part, normally a user with most common threat models should not need to bother as long as windows shows a “verified publisher”
Hope that explains it a bit more.
Best Regards,
Andre
I am attempting to go through the same process, using Microsoft’s signing tool with Window 10 SDK. Here is what I get, but I am also unable to match these against the signatures I found on your package integrity page (Gpg4win - Check Integrity
Verifying: C:\Users\directory\Downloads\GPG\gpg4win-4.2.0.exe
Signature Index: 0 (Primary Signature)
Hash of file (sha256): 07C67D1492F95FEDE31B626F30D1E630AFA19B66ACBC34D3111FF1F4014A7303
Signing Certificate Chain:
Issued to: GlobalSign Code Signing Root R45
Issued by: GlobalSign Code Signing Root R45
Expires: Fri Mar 17 16:00:00 2045
SHA1 hash: 4EFC31460C619ECAE59C1BCE2C008036D94C84B8
Issued to: GlobalSign GCC R45 CodeSigning CA 2020
Issued by: GlobalSign Code Signing Root R45
Expires: Sat Jul 27 16:00:00 2030
SHA1 hash: 7A2146EDB29E2EAD64AFBE7CEAD0B6085D437A32
Issued to: g10 Code GmbH
Issued by: GlobalSign GCC R45 CodeSigning CA 2020
Expires: Wed Jul 02 04:12:13 2025
SHA1 hash: B2852D4490F655EBEADF9FFD8D092E8154450077
The signature is timestamped: Fri Jul 14 03:40:34 2023
Timestamp Verified by:
Issued to: GlobalSign
Issued by: GlobalSign
Expires: Sun Mar 18 02:00:00 2029
SHA1 hash: D69B561148F01C77C54578C10926DF5B856976AD
Issued to: GlobalSign
Issued by: GlobalSign
Expires: Sun Mar 18 02:00:00 2029
SHA1 hash: 618A4F66F2AB56AF464B0C3697F6F1C91F88F8B4
Issued to: GlobalSign Timestamping CA - SHA384 - G4
Issued by: GlobalSign
Expires: Sat Dec 09 16:00:00 2034
SHA1 hash: F585500925786F88E721D235240A2452AE3D23F9
Issued to: Globalsign TSA for Advanced - G4
Issued by: GlobalSign Timestamping CA - SHA384 - G4
Expires: Sat May 07 23:44:12 2033
SHA1 hash: 9F20DEAB9E36D5020A8CCC0530387C687F2AD1C7
Successfully verified: C:\Users\directory\Downloads\GPG\gpg4win-4.2.0.exe
Number of files successfully Verified: 1
Number of warnings: 0
Number of errors: 0
Acutally, re-reading your response, it look like I have a match between the following
SHA1 hash: B2852D4490F655EBEADF9FFD8D092E8154450077 (my verification result)
sha_fpr: B2:85:2D:44:90:F6:55:EB:EA:DF:9F:FD:8D:09:2E:81:54:45:00:77 (package integrity wiki)
Just to confirm, is this the most important values to match?
Hopefully, this is the last set of questions. Can you tell me if I am doing something wrong, or if there is an additional step that I need to take.
Trying to verify OpenPGP Signature as described in this page
Gpg4win/CheckIntegrity - GnuPG wiki
I tried via command line, as described in these instructions, but got that gpg could not open gpg4win*.exe.sig
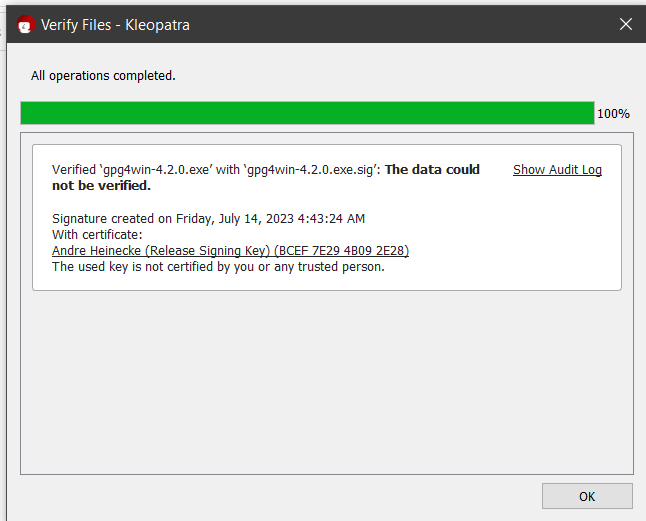
So, I opened Kleopatra and attempted to verify signature that way. Below is an image of the result, as well at the GPG Audit Log.
gpg: Signature made 7/14/2023 4:43:24 AM Pacific Daylight Time
gpg: using RSA key 5B80C5754298F0CB55D8ED6ABCEF7E294B092E28
gpg: Good signature from “Andre Heinecke (Release Signing Key)” [unknown]
gpg: WARNING: This key is not certified with a trusted signature!
gpg: There is no indication that the signature belongs to the owner.
Primary key fingerprint: 5B80 C575 4298 F0CB 55D8 ED6A BCEF 7E29 4B09 2E28
Looks like I need to import
GnuPG - Signature Key
Hi @greyswan ,
welcome to the GnuPG / Gpg4win Forum!
Verifying: C:\Users\directory\Downloads\GPG\gpg4win-4.2.0.exe
Signing Certificate Chain:
Issued to: g10 Code GmbH
Expires: Wed Jul 02 04:12:13 2025
SHA1 hash: B2852D4490F655EBEADF9FFD8D092E8154450077
matches what is the current signing certificate listed on Gpg4win - Check Integrity .
So you know that the installer is the one that the website gpg4win.org marks as official. This is the most important part, you did well.
I’ve just updated https://wiki.gnupg.org/Gpg4win/CheckIntegrity to be more clear on what is enough, let me know if this would have worked better for you.
Note that our instructions are general. Some people have very high security needs and do more checks to defend against different potential attacks. This often is too much because if you cannot trust the operating’s verification mechanisms anymore, you’ll have other things to worry about. ![]()
Best Regards,
Bernhard
@bernhard - Thank you very much for the replies and the confirmation.
A couple additional suggestions that would have helped me on the Wiki page:
-
I didn’t realize that the sha1_fpr key was actually the pubkey that I was supposed to match. Clarifying that for newbies would be great.
-
Also, trying to simply find, download and install the MS Signtool was not simple. Had to go thru a few different forum posts to find out where to get the appropriate download file, and how to install only the signtool and not all the other SDK apps. Turned out it was quite simple once I actually located the file, but I was trying to make sure that I understood the entire process process before downloading anything.
Last followup questions.
a) Do I need to self-certify the author signature keys to complete the certification process?
b) It seems that I must create my own private/public key pair in order to self-certify. I haven’t created those yet as I wasn’t clear if I could save those to USB or other device that I can airgap (don’t want those key’s anywhere on my internal drives)?
Thanks again.
Thanks for your feedback @greyswan!
I have further improved the wiki page. Adding a mention of sha1_fpr and used a newer link to Microsoft’s signtool. However Microsoft sometimes changes its documentation and there are probably several ways to get the signtool. The page we link to says that it is available with the SDK, so that is the best we can do to point to the page Microsoft has prepared for people who are interested in SignTool.
Do I need to self-certify the author signature keys to complete the certification process?
If you mean as part of the verification process if you want to (optionally) check the OpenPGP signature on the installer? No.
b) It seems that I must create my own private/public key pair in order to self-certify.
I am not entirely sure what you mean by self-certify. If you want to locally sign the Gpg4win public key (aka “pubkey”) to indicate that you have checked it, you can do so, but it only gains you something for the next time where you do not need to do your checks again. As you would be “certifying” the Gpg4win pubkey it wouldn’T be a classical “self-certification”.
Anyhow to verify that the Gpg4win installer you have is the one officially published by the makers of the gpg4win.org website and the company g10 code GmbH, checking the code signing is completely sufficient. Checking the OpenPGP signature is purely optional if you do not trust the website, your system and you have a different way to get get more trust into the pubkey.
(I know all these “trust” issues are complex topic.)
Best Regards,
Bernhard
Thank you again for being so prompt and complete in your responses.
Just to clarity, when I said: “b) It seems that I must create my own private/public key pair in order to self-certify,” I was referring to the process below. My question is, where can I store that GPG key? Can I push GPK key to USB, or even use something like a Yubikey, to create
"Generating a New GPG Key
If you’re reading this, chances are you don’t have a GPG key yet. Let’s generate a new one for signing commits and tags."
Best to open a new discussion topic for this one, as it is unrelated to “verifiying Gpg4win”. ![]()